Compiling TrueCrypt on Raspberry Pi
Monday, 21 January 2013
These steps were gleaned from the work completed by Reinhard Seiler.
Other than the manual download and placement of the TrueCrypt source, the rest should be fairly hands off. So first, get the “TrueCrypt 7.1a Source.tar.gz” package from http://www.truecrypt.org/downloads2 and copy it to /usr/local/src/ on the Raspberry Pi.
Secondly, run the commands below, oh, and at your own risk of course… 🙂
#!/bin/bash #get source files other than the TrueCrypt source sudo wget -P /usr/local/src http://prdownloads.sourceforge.net/wxwindows/wxWidgets-2.8.11.tar.gz sudo wget -P /usr/local/src/pkcs11 ftp://ftp.rsasecurity.com/pub/pkcs/pkcs-11/v211/pkcs11.h sudo wget -P /usr/local/src/pkcs11 ftp://ftp.rsasecurity.com/pub/pkcs/pkcs-11/v211/pkcs11f.h sudo wget -P /usr/local/src/pkcs11 ftp://ftp.rsasecurity.com/pub/pkcs/pkcs-11/v211/pkcs11t.h #get and install dependent packages sudo apt-get -y install libgtk2.0-dev libfuse-dev nasm libwxgtk2.8-dev #extract, configure, and make wxWidgets sudo tar -xzvf /usr/local/src/wxWidgets-2.8.11.tar.gz -C /usr/local/src cd /usr/local/src/wxWidgets-2.8.11/ ./configure make #setup, extract export PKCS11_INC=/usr/local/src/pkcs11 sudo tar -xzvf /usr/local/src/TrueCrypt 7.1a Source.tar.gz -C /usr/local/src cd /usr/local/src/truecrypt-7.1a-source #comment out some lines that prevented building sed -i 's#TC_TOKEN_ERR (CKR_NEW_PIN_MODE)#/*TC_TOKEN_ERR (CKR_NEW_PIN_MODE)*/#g' Common/SecurityToken.cpp sed -i 's#TC_TOKEN_ERR (CKR_NEXT_OTP)#/*TC_TOKEN_ERR (CKR_NEXT_OTP)*/#g' Common/SecurityToken.cpp sed -i 's#TC_TOKEN_ERR (CKR_FUNCTION_REJECTED)#/*TC_TOKEN_ERR (CKR_FUNCTION_REJECTED)*/#g' Common/SecurityToken.cpp #compile, build, make! sudo make WX_ROOT=/usr/local/src/wxWidgets-2.8.12/ wxbuild sudo -E make WXSTATIC=1 echo echo TrueCrypt should be found in /usr/local/src/truecrypt-7.1a-source/Main/
Finally, copy the compiled ‘truecrypt’ binary from /usr/local/src/truecrypt-7.1a-source/Main/ to /usr/local/bin/.
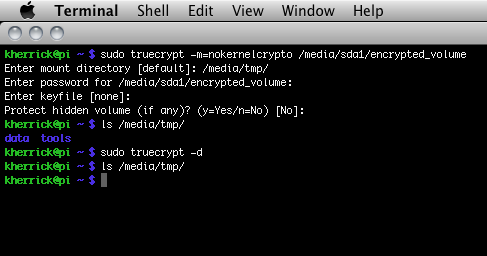
Afterwards, I was able to run it from the command line and view the help. There are two items in particular that may be of interest for those going through these steps. One is, when attempting to mount an encrypted volume with the Raspberry Pi that I have, I received the following:
Error: device-mapper: reload ioctl on truecrypt1_1 failed: No such file or directory Command failed
It appears as though it may be due to a particular kernel module not being compiled in. So I added the “-m=nokernelcrypto” command line option and was successful.
For more command line usage, see their website @ http://www.truecrypt.org/docs/?s=command-line-usage. I haven’t tested it yet, but it should work graphically as well.
Also, though some may not want to edit the source directly, I ended up commenting out lines 660, 661, and 662 of /usr/local/src/truecrypt-7.1a-source/Common/SecurityToken.cpp in order for the compile to work (see the sed lines in the script I provided above). Here’s the difference between the original and the changed source:
diff ./SecurityToken.cpp /usr/local/src/truecrypt-7.1a-source/Common/SecurityToken.cpp 660,662c660,662 < TC_TOKEN_ERR (CKR_NEW_PIN_MODE) < TC_TOKEN_ERR (CKR_NEXT_OTP) < TC_TOKEN_ERR (CKR_FUNCTION_REJECTED) --- > /*TC_TOKEN_ERR (CKR_NEW_PIN_MODE)*/ > /*TC_TOKEN_ERR (CKR_NEXT_OTP)*/ > /*TC_TOKEN_ERR (CKR_FUNCTION_REJECTED)*/
While there are some compromises in the process described above, it was the only way I could get it compiled in the time I allotted to the task.
